THE HARDENING BRIEF | Issue #002 Weekly security findings for sysadmins.
The Finding
By default every Windows machine running Remote Desktop generates a self-signed certificate that no client can actually verify. When a user connects and clicks through that "the identity of the remote computer cannot be verified" warning, an attacker sitting between them and the server can intercept the entire session, capture credentials, and the user will never know. This is not theoretical. Tools exist that automate RDP MITM attacks by presenting a forged certificate to the client while proxying the real connection silently in the background. The fix is deploying a proper certificate from your internal CA via Group Policy so clients can actually verify they are talking to the right machine.
One important nuance before you start: this requires Active Directory Certificate Services already running in your environment. If you are using a standalone CA or no CA at all, the GPO-based autoenrollment approach will not work and you will need to assign certificates manually.
The Fix
Step 1 — Create the certificate template (certtmpl.msc)
Open the Certificate Templates console on your CA server. Duplicate the Workstation Authentication template and configure as follows:
Compatibility tab
CA: Windows Server 2008
Certificate recipient: Windows Vista
General tab
Template display name and template name: identical values
Example: RemoteDesktopAuthentication (no spaces)
Validity period: 6 to 12 months
Renewal period: minimum 5 weeks
Request Handling tab
RSA key: Signature and Encryption
ECDSA key: Signature only
Cryptography tab
Provider category: Key Storage Provider
Provider: Microsoft Software Key Storage Provider
Extensions tab
Application Policies: click Edit
Remove: Client Authentication
Add new EKU:
Name: Remote Desktop Authentication
OID: 1.3.6.1.4.1.311.54.1.2
Security tab
Domain Computers: Read + Enroll
Domain Controllers: Read + Enroll

Step 2 — Configure the GPO (gpmc.msc)
Create a new GPO and link it to the OUs containing your RDP hosts. Navigate to:
Computer Configuration → Policies → Windows Components
→ Remote Desktop Services → Remote Desktop Session Host
→ Security
→ Server authentication certificate template
→ Enabled
→ Certificate Template name: RemoteDesktopAuthentication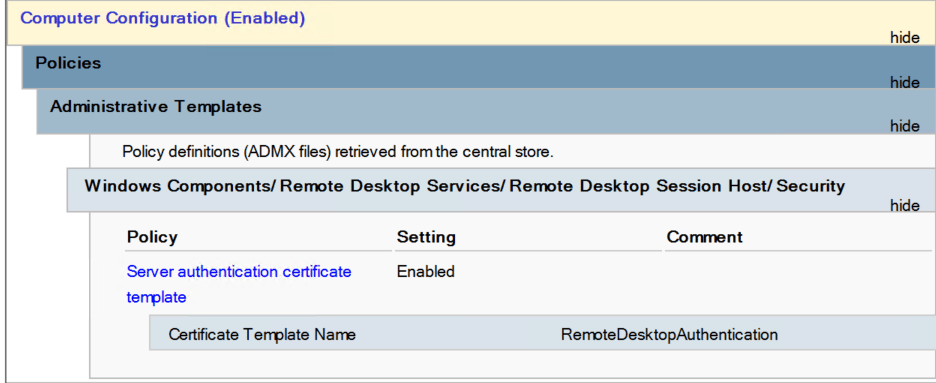
Run gpupdate /force and certutil.exe -pulse on a test machine after linking.
Step 3 — Verify it worked (PowerShell)
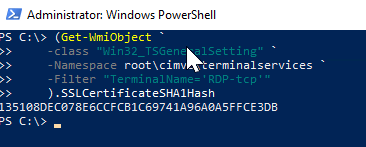
Run this on any RDP host after GPO has applied:
(Get-WmiObject `
-class "Win32_TSGeneralSetting" `
-Namespace root\cimv2\terminalservices `
-Filter "TerminalName='RDP-tcp'"
).SSLCertificateSHA1HashTake the returned thumbprint and open certlm.msc on the same machine. Find the certificate under Remote Desktop. The issuer should show your internal CA, not the machine itself.

One Action Today
Run the PowerShell command above on any machine in your environment that accepts RDP connections and check whether the issuer is your CA or the machine itself. 🔑
